Events
On-demand events

Deploying Spring Boot Applications on Istio
Join Tetrate’s Eitan Suez in an exploration of deploying and running Spring Boot microservices on top of Istio. Prior to the advent of service mesh, the predominant way Enterprise Java…
Read More arrow_forward
5 Stages to Istio Production Success
Join us as we venture into the world of Istio production! With cloud native experts from both Venafi and Tetrate as your guides, you’ll learn the 5 stages of successfully…
Read More arrow_forward
Istio 0-60 Workshop
This workshop consists of a series of labs that together comprise a hands-on tour of Istio “from 0 to 60,” so to speak. If you want to get a better…
Read More arrow_forward
An Update on NIST Zero Trust Guidelines and FIPS Compliance
Application architectures are increasingly distributed and decentralized for performance and resilience. This brings unknown risks and new challenges to protect them. Zero Trust security has emerged as an effective framework…
Read More arrow_forward
Zero Trust at Runtime: An Update on NIST SP 800-207A
As technology evolves and cyber threats become increasingly sophisticated, staying up-to-date with the latest security standards is imperative for organizations. In this webinar, Zack Butcher and Ramaswamy Chandramouli will provide…
Read More arrow_forward
Data Protection in the Mesh with Tetrate and LeakSignal
In this joint webinar with Tetrate and LeakSignal, we unveil how these two powerful solutions seamlessly collaborate to fortify data protection within your mesh environments. Join us for a technical…
Read More arrow_forward
Istio Office Hours for AWS Users: Securing Your Application Networks on EKS
Join us for an exclusive office hours session dedicated to exploring the powerful security capabilities of Istio on Amazon EKS! We will review Istio distros and TSE’s cutting-edge service security…
Read More arrow_forward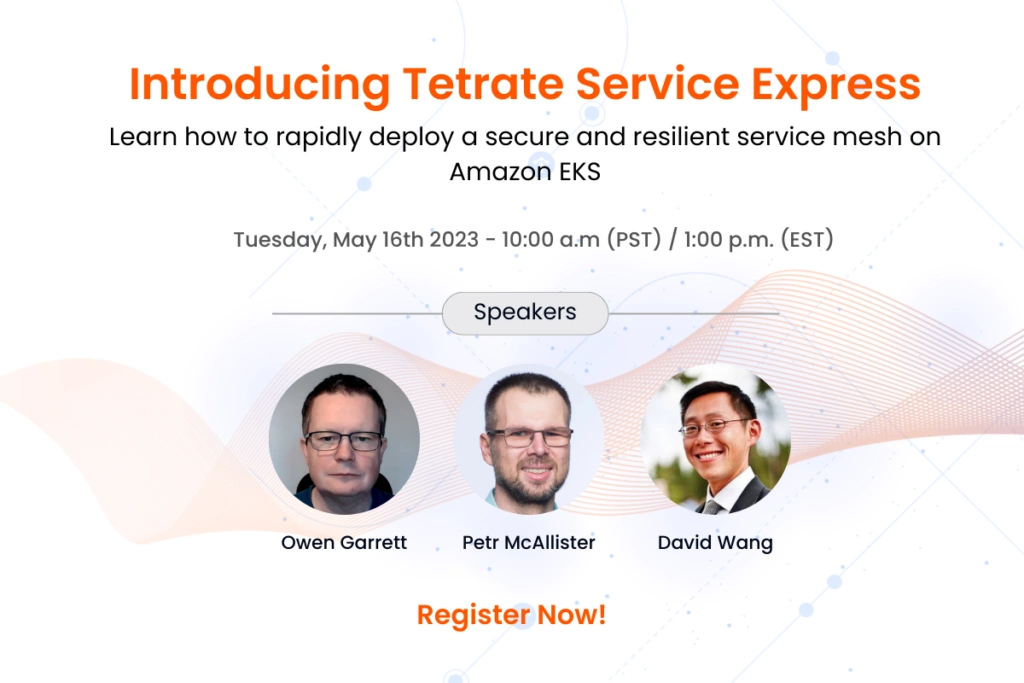
Introducing Tetrate Service Express
The fast track to a secure and resilient service mesh on Amazon EKS Getting your first Istio-based service mesh up and running is hard, and achieving resilience and security for…
Read More arrow_forward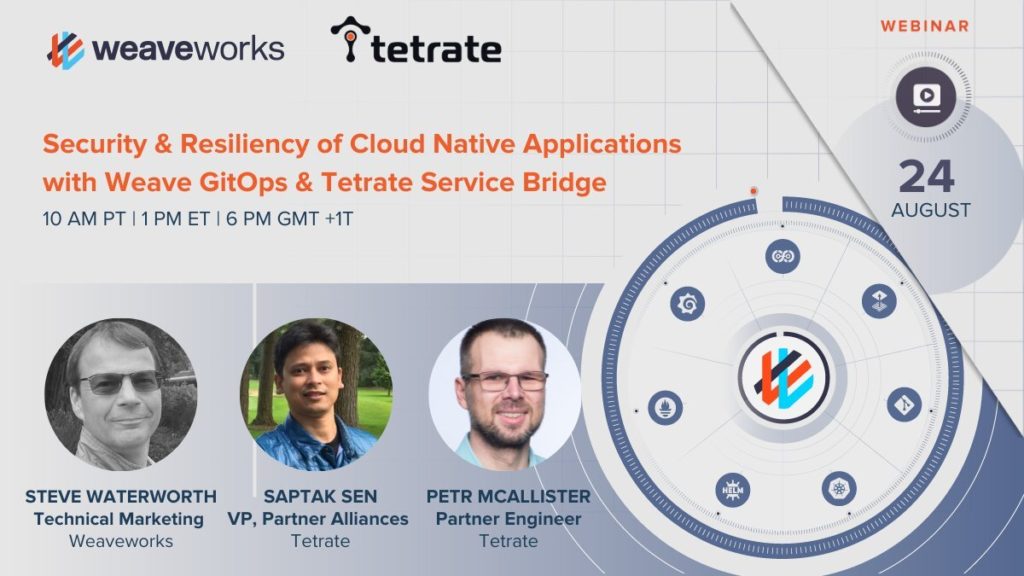
Security and Resiliency of Cloud Native Applications with Weave GitOps and Tetrate Service Bridge
Cloud-native applications are increasingly spanning across hybrid and multi-cloud environments such as on-premise data centers, in the cloud (Amazon EKS, Azure AKS, Google Cloud GKE) and at the edge. Customers…
Read More arrow_forward