Introducing Tetrate Config Analyzer (TCA)
As Istio’s adoption continues to grow, managing and maintaining service mesh configurations becomes increasingly critical. Whether you’re deploying in production or experimenting in a development environment, having accurate configurations

As Istio’s adoption continues to grow, managing and maintaining service mesh configurations becomes increasingly critical. Whether you’re deploying in production or experimenting in a development environment, having accurate configurations is key to avoiding downtime, security vulnerabilities, or unexpected behaviors.
Enter Tetrate Config Analyzer (TCA) — a command-line tool designed to simplify, verify, and ensure best practices for Istio service mesh deployments. Built for ease-of-use, TCA is part of the Tetrate Istio Subscription (TIS), a commercial solution that provides enterprise-grade capabilities to make service mesh simpler and more robust.
TCA empowers users—be they administrators, developers, or DevOps professionals—to verify their Istio configurations effortlessly. By applying best practices, identifying potential issues, and providing guidance on configuration corrections, TCA offers a proactive approach to Istio configuration management.
For a more detailed guide on avoiding common Istio misconfigurations, you can refer to our blog post: Istio Configuration Security: How to Avoid Misconfigurations.
TCA addresses these challenges by providing:
- Comprehensive Configuration Validation: automatically detect Istio configuration issues based on best practices
- Actionable Insights & Recommendations: receive a report and a session to explain configuration issues & provide targeted recommendations for optimization
- On-Demand Analysis for Pre-Deployment Assurance: upload and analyze YAML files before deploying changes, reducing configuration errors and ensuring smooth, reliable updates to production environments
How TCA Works
TCA operates as a standalone command-line tool, analyzing Istio configuration files or live Kubernetes clusters. It processes all the Istio resources in the environment and generates a comprehensive report of any errors or warnings it detects.
Here is an example of the output of the TCA analyzer.
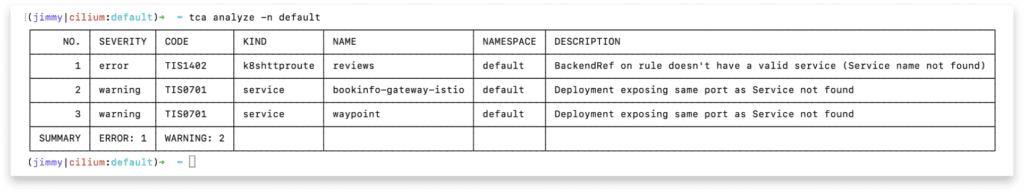
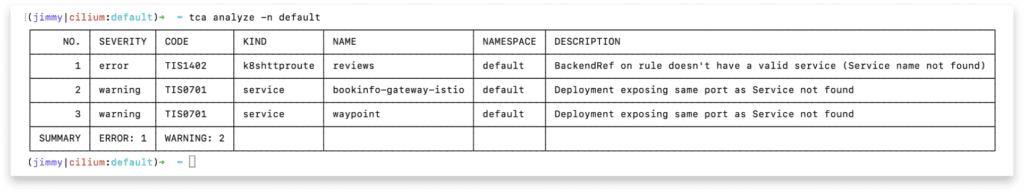
Report Types
- Errors: Critical issues requiring immediate attention, such as misconfigured security policies or incorrect traffic routing.
- Warnings: Non-critical but concerning configuration issues that might affect efficiency or adherence to best practices.
TCA offers not only an analysis of the problem but also helpful suggestions for remediation. It’s designed to reduce the guesswork in identifying and solving configuration issues, helping users avoid costly downtime. For a complete list of configuration checks that TCA performs, see our configuration analysis documentation.
Key Use Cases
TCA is valuable in a number of different scenarios:
- Training: Use TCA as a teaching tool to familiarize team members with common configuration pitfalls and best practices for Istio.
- CI/CD Integration: Validate Istio configurations as part of your deployment pipeline, ensuring that changes follow best practices.
- Ongoing Maintenance: Schedule regular audits of Istio deployments to ensure configurations remain healthy over time, especially as your cluster evolves.
- Incident Management: When things go wrong, TCA helps pinpoint the root causes related to misconfiguration, so issues can be resolved faster.
Getting Started with TCA
You can start using Tetrate Config Analyzer in a few easy steps:
- Download and Install the TCA binary for Linux, macOS, or Windows.
- Set up your kubectl context to connect to the desired Kubernetes cluster.
- Run TCA using tca analyze to get your first configuration analysis report.
Example Usage
Running TCA is straightforward and efficient:
- To analyze all namespaces in the current cluster context:
tca analyze - To analyze a specific namespace:
tca analyze -n my-namespace - To run an analysis locally to identify potential issues before applying configuration files to a cluster, similar to a dry-run:
tca analyze --local-only -f /path/to/mesh-config.yaml
TCA also provides multiple output options (JSON, YAML, and table) to help you seamlessly integrate it into your workflow or other tooling.
Future Roadmap
Looking ahead, we’re excited to expand TCA’s capabilities based on our extensive experience with enterprise Istio deployments. Our roadmap is shaped by common challenges we’ve observed across our customer base, focusing on enhancing security validation, streamlining configuration management, and simplifying the adoption of service mesh best practices. We’re committed to making TCA an even more powerful tool that helps teams confidently manage their service mesh configurations at scale.
Get Involved and Start Testing
TCA is available as part of Tetrate Istio Subscription (TIS). Existing TIS customers can start using TCA right away. For organizations interested in TCA’s capabilities, contact us to learn more about TIS and how it can help your organization manage service mesh configurations more effectively.
For more details on how to access TCA, please visit the official documentation.








